Introduction
Windows 10 Timeline is a relatively new forensic artefact, which was introduced in Windows 10 version 1803.
Timeline helps to track users´ activities. You can find here information about files opened by user, applications he used or websites he visited. Purpose of Windows 10 Timeline is to allow user to quickly resume his recent activities. Windows 10 Timeline can be synchronized across all devices to which user authenticates with same account.
Timeline is for forensic analyst an invaluable source of information about user activity, not limited to local system. Information about file opening, applications usage, or copy-pasting something is provided with timestamps. One important note: not all actions are recorded in Windows 10 Timeline. You should not take this artifact as a single and complete source of data about users´ activity.
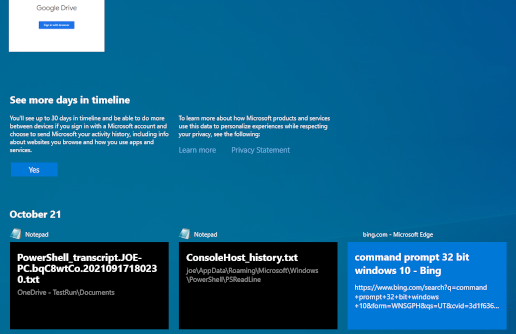
You can display Timeline by clicking on icon (highlighted in green) placed in Desktop taskbar, right to the Start button and Search bar.
Picture 1: Windows 10 Timeline icon
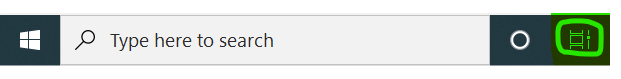
After you click on the icon, activity history from last 30 days will display to you. 30 days is default time span from which are data recorded in Timeline.
Observe the information for user: it offers an opportunity to sync his activity to the cloud.
Picture 2: Displaying user´s activities
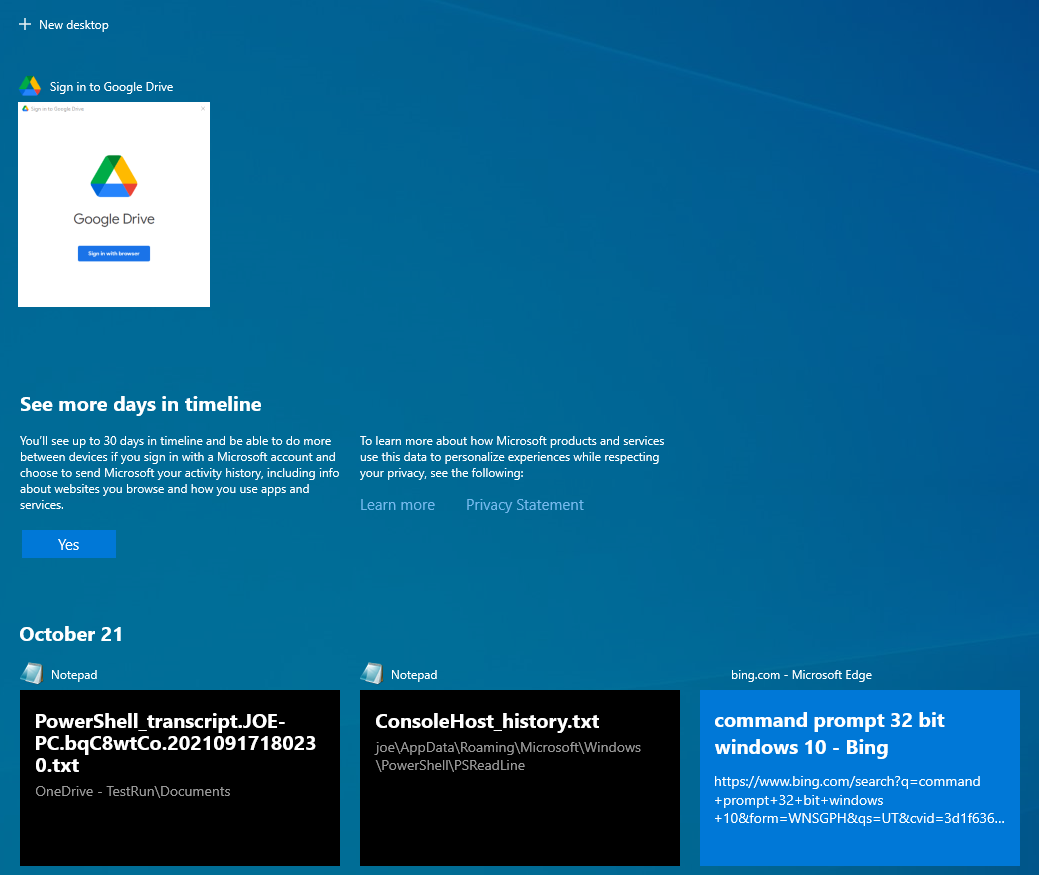
Windows 10 Timeline Settings
We can influence the way how is Windows 10 Timeline populated and its synchronization to cloud either during Windows OS installation, or (after installation) from System Settings.
Creation of Windows 10 Timeline is configured in system settings, in section Privacy → Activity History. Specific settings can differ on various Windows versions. In our test environment were two options available:
- Store my activity history on this device – stores activity history on local device only
- Send my activity history to Microsoft – induces synchronization of activity data with MS cloud
Picture 3: W10 Timeline Settings
Windows 10 Timeline on a disk
Data from the Timeline are stored on disk in user profile directory – in folder %userprofile%\AppData\Local\ConnectedDevicesPlatform\. User´s activity is stored in folder L.<username>, for example L.joe. Information is recorded in SQLite database ActivitiesCache.db.
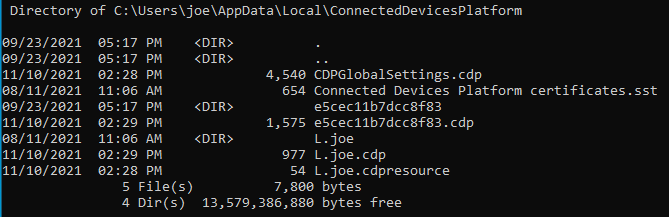
Picture 4: Content of folder ConnectedDevicesPlatform
File L.joe.cdp contains information used by a service named Connected Devices Platform. It is a relatively new service, present only in newer Windows OS versions. Among its other functions, CDP plays a role in connecting Bluetooth devices, printers, scanners, as well as smartphones, music players, cameras and similar. CDP service allows devices such as smartphones and computers to recognize each other and exchange notifications.
If the Timeline is set to sync with cloud, you will find information about last synchronization (CNCNotificationUriLastSynced) and user´s ID in .cdp file. If the value CNCNotificationUriLastSynced is zero, Timeline is not being synced.
ActivitiesCache.db is an SQLite database. SQLite is one of the most used database formats worldwide. It is a relational database, which does not have client-server architecture but is embedded in a program. SQLite format is used by popular internet browsers such as Google Chrome, Mozilla Firefox and others. Database is comprised of one file and can have an associated WAL file (the abbreviation stands for write-ahead log).
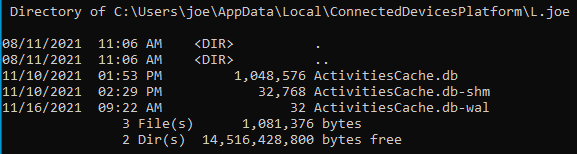
Picture 5: Content of folder L.joe
ActivitiesCache.db contains multiple tables. How are individual records added to the database during user´s interaction with the system?
- User opens a file or performs another activity on the system.
- A new and unique Activity ID is generated.
- A record is created in Activity_PackageId.
- A record is created in ActivityOperation table.
- Depending on sync settings, activity is or is not synchronized to the cloud.
- A new activity record is added to the table Activity.
- Activity is removed from ActivityOperation table.
Two tables which are the most important for forensic analysis are Activity and Activity_PackageID.
Analysis of ActivitiesCache.db
Let us open the Windows 10 Timeline database in a tool for browsing SQLite database (such as DB Browser for SQLite¹) and inspect the contents of Activity_PackageID table:
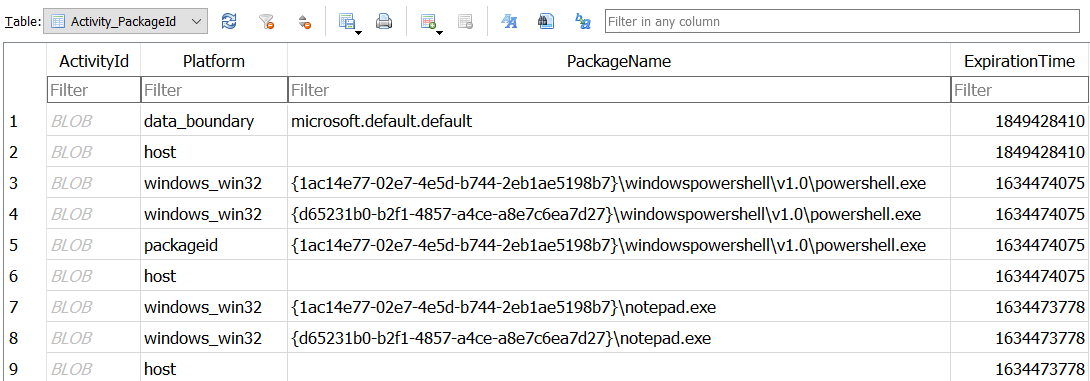
Picture 6: Activity_PackageID table
The table contains records about applications – or, more precisely, application packages, responsible for activity: file name, path to the application´s executable file and expiration time of records. Expiration time is set to 30 days from the last application´s usage and is stored in UNIX epoch time format (integer representing number of units – in this case seconds – elapsed since midnight 1st January 1970). Records are stored for 30 days. Records related to files which are not on the disk anymore are preserved in timeline: this might be incredibly useful for an analyst trying to prove presence of or operation with some file at a certain point of time.
Table Activity contains detailed records about user´s activity. See the preview of its content in SQLite browser:
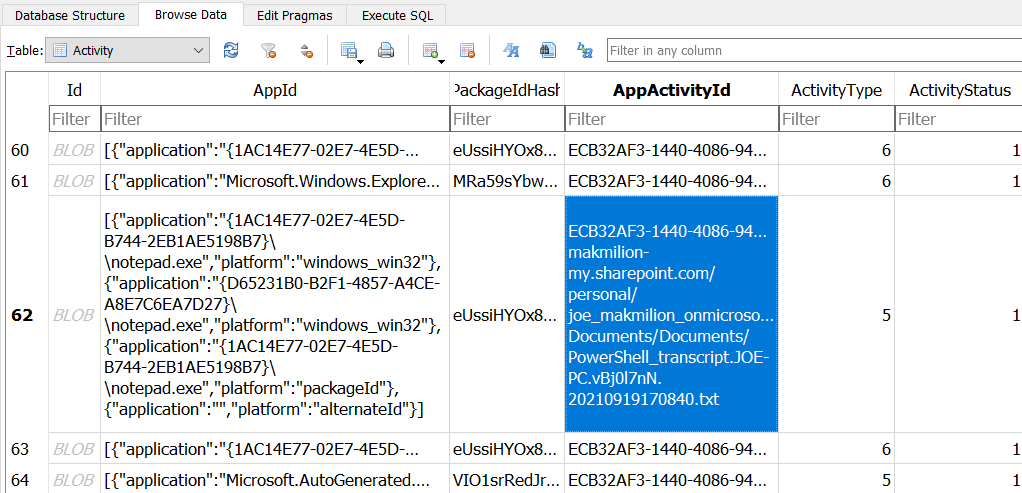
Picture 7: Activity table
Let´s talk a bit about individual parameters recorded for each table entry:
- AppId – application/application package from Activity_PackageId table which generated the activity record
- AppActivityId – identifier specific for activity; it indicates where the activity should be resumed when the user decides to come back to it. It can be a URL, a file path, …
- Timestamps – self explaining 😊 again, they are preserved in UNIX Epoch time format:
- Start Time – time when the activity began
- End Time – time when the activity finished
- Last Modified Time – time when the activity has been last modified
- Expiration Time – activities’ expiration time, most often 30 days since creation or modification of activity
- ActivityType: can have multiple values, for example
- 5 – user opened an application (it is a new activity, user does not resume previous activity: for example, when you open Notepad, it is a new activity of type 5; however, it does not mean that you did not open Notepad before, so „new“ activity does not mean „the first usage“ of certain app on the system)
- 6 – user was working with an app again, for example he came back to opened Notepad window; for this ActivityType, time zone is included in the Payload filed
- 10 – Copy/Paste – unfortunately, we were not able to reproduce this type of activity during our tests. Therefore, we refer to available sources² for description: Payload field might not be available, but we should be able to find Base64 encoded text copied to clipboard in field ClipboardPayload. This data is not available for 30 days, precise lifespan is not even known: it is possibly 12 days. More testing and investigating should be performed to get better understanding of this artefact. However, its potential for investigation is obvious.
- 16 – Copy/Paste, another interesting ActionType: it is distinguishable by field „Group“, which contains either value „Copy“ or „Paste“. Payload field mentions GDPR. You can find an ID of application, from which data were copied, in the field ParentActivityId.
- ActivityStatus:
- 1 – active
- 2 – updated; always when the activity is updated (some of its parameters changed, for example user read the document further than before), Expiration Time is reset to 30 days
- 3 – deleted
- 4 – ignored
- ETag: so-called event ordering integer: during the change of individual table entry, a new etag is generated and is assigned to the table row which changed. This parameter is useful for identifying an order of activity execution.
- In Payload field we can notice a parameter „activeDurationSeconds“: it records how long the user interacted with the application in the during that specific action: for example, how long has PowerShell_ISE been opened.
- PlatformDeviceId – content can be corelated with registry key NTUSER.DAT\Software\Microsoft\Windows\CurrentVersion\TaskFlow\DeviceCache.
This key contains subkeys representing values from PlatformDeviceId; it contains value DeviceName. We were not successful in replicating the key DeviceCache during the tests. Included information are from external sources².
Values of DeviceType allow us to distinguish between various devices which could be synced:- 1 Xbox One
- 6 Apple iPhone
- 7 Apple iPad
- 8 Android device
- 9 Windows 10 Desktop
- 11 Windows 10 Phone
- 12 Linux device
- 13 Windows IoT
- 14 Surface Hub
- 15 Windows Laptop
If we wanted to create a screenshot containing all the fields, it would be quite wide 😊 We probably do not plan to analyze such extensive artefact as Windows 10 Timeline manually. Tools exist which allow parsing and exporting data from Windows 10 Timeline to readable format.
One of favorite tools is W10TCmd.exe³, written by security researcher Eric Zimmerman.
Like other tools authored by Mr. Zimmerman, we can save the output in CSV file.
WxTCmd.exe -f <path>\ActivitiesCache.db --csv \<outputdir>\
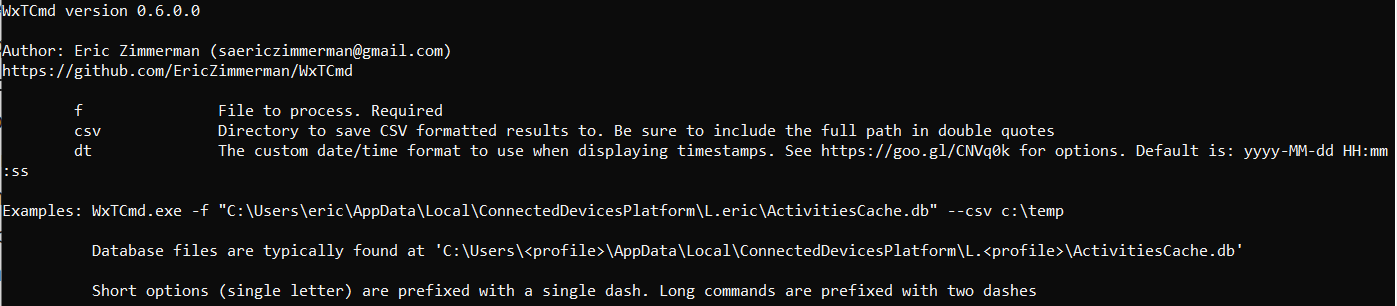
Picture 8: Usage of WXTCmd.exe
Let´s look at the output of the tool. Observe ActivityType 5 and 6 in second and third line.
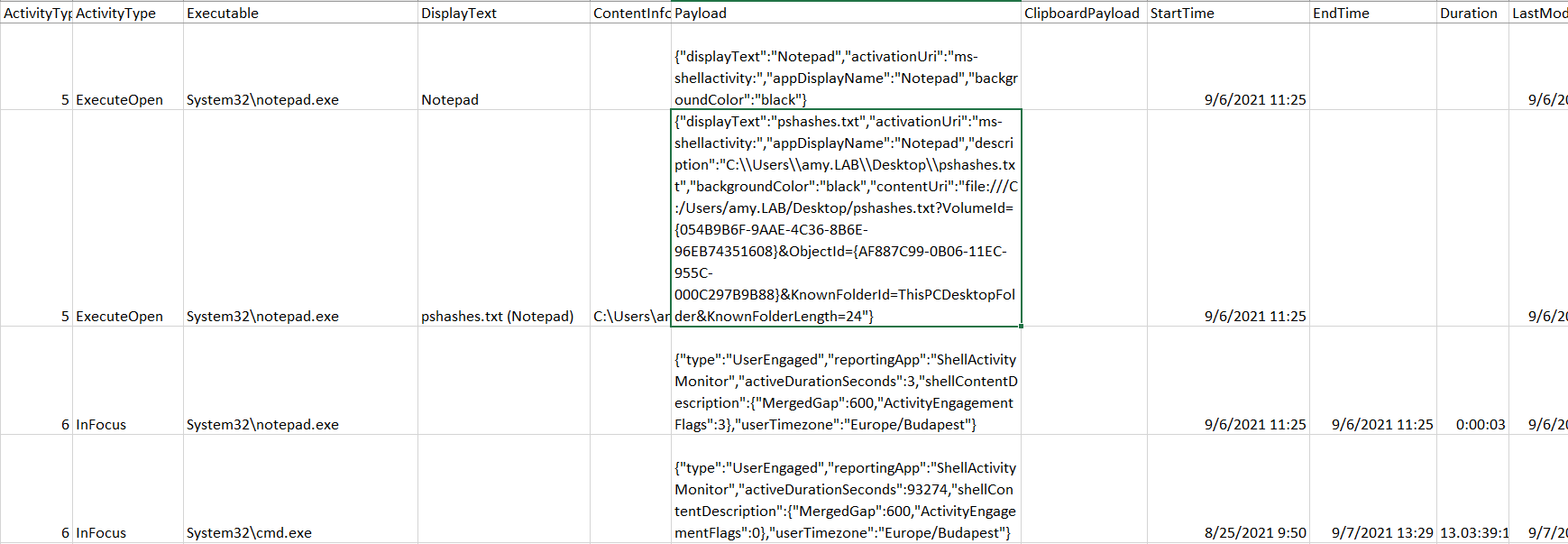
Picture 9: Output from WXTCmd.exe
Activity of type 5 – ExecuteOpen – is created as first. This corresponds to opening an application package responsible for the action, Notepad.exe in this case. Name of file opened using Notepad is in the DisplayText field: pshashes.txt. Finally, full path of the opened file is in Payload field.
Activity of type 6 – InFocus – follows. Start time is same as for previous Type 5 activity. Activity has been finished and lasted for 3 seconds (see Duration field). This means that user, from whose profile this Activity table comes from, opened file pshashes.txt from C:\Users\amy.LAB\Desktop\pshashes.txt using application Notepad with executable in System32\notepad.exe. The relation lasted 3 seconds.
Look at the record about activity System32\cmd.exe. Apparently, command line has been opened for more than 13 days 😊
In activities of type 6 – InFocus – there is time zone information included in Payload field. In this case we can see that device from which activity comes is in Europe\Budapest time zone. This corresponds to UTC + 2 at the date where the record was created.
Finally, let´s look at all details which were recorded about activity related to web browsing. User entered term „command prompt 32 bit windows 10“ to the search bar of Microsoft Edge. Executable package is Microsoft.MicrosoftEdge_8wekyb3d8bbwe!MicrosoftEdge – not standard .exe file.
Id: 2766239d-4de6-206e-8e5c-9df417aad45d
ActivityTypeOrg: 5
ActivityType : ExecuteOpen
Executable: Microsoft.MicrosoftEdge_8wekyb3d8bbwe!MicrosoftEdge
DisplayText: command prompt 32 bit windows 10 - Bing (Microsoft Edge)
ContentInfo:
https://www.bing.com/search?q=command+prompt+32+bit+windows+10&form=WNSGPH&qs=UT&cvid=3d1f6366c54b46a6903fc869fa9369f1&pq=command+prompt+32&cc=SK&setlang=en-US&nclid=D9455599751C3BE1DD1D7DD2011D2BB0&ts=1634819645424&wsso=Moderate (https://www.bing.com/search?q=command prompt 32 bit windows 10&form=WNSGPH&qs=UT&cvid=3d1f6366c54b46a6903fc869fa9369f1&pq=command prompt 32&cc=SK&setlang=en-US&nclid=D9455599751C3BE1DD1D7DD2011D2BB0&ts=1634819645424&wsso=Moderate)
Payload:
{"displayText":"command prompt 32 bit windows 10 - Bing","activationUri":"microsoft-edge:https://www.bing.com/search?q=command+prompt+32+bit+windows+10&form=WNSGPH&qs=UT&cvid=3d1f6366c54b46a6903fc869fa9369f1&pq=command+prompt+32&cc=SK&setlang=en-US&nclid=D9455599751C3BE1DD1D7DD2011D2BB0&ts=1634819645424&wsso=Moderate","appDisplayName":"Microsoft Edge","description":"https://www.bing.com/search?q=command+prompt+32+bit+windows+10&form=WNSGPH&qs=UT&cvid=3d1f6366c54b46a6903fc869fa9369f1&pq=command+prompt+32&cc=SK&setlang=en-US&nclid=D9455599751C3BE1DD1D7DD2011D2BB0&ts=1634819645424&wsso=Moderate","backgroundColor":"#FF0078D7","adaptiveContent":{"$schema":"http://adaptivecards.io/schemas/adaptive-card.json","type":"AdaptiveCard","version":"1.0","body":[{"type":"Container","items":[{"type":"TextBlock","text":"command prompt 32 bit windows 10 - Bing","weight":"bolder","size":"large","wrap":true,"maxLines":3},{"type":"TextBlock","text":"https://www.bing.com/search?q=command+prompt+32+bit+windows+10&form=WNSGPH&qs=UT&cvid=3d1f6366c54b46a6903fc869fa9369f1&pq=command+prompt+32&cc=SK&setlang=en-US&nclid=D9455599751C3BE1DD1D7DD2011D2BB0&ts=1634819645424&wsso=Moderate","size":"normal","wrap":true,"maxLines":3}]}]},"contentUri":"https://www.bing.com/search?q=command+prompt+32+bit+windows+10&form=WNSGPH&qs=UT&cvid=3d1f6366c54b46a6903fc869fa9369f1&pq=command+prompt+32&cc=SK&setlang=en-US&nclid=D9455599751C3BE1DD1D7DD2011D2BB0&ts=1634819645424&wsso=Moderate","attribution":{"iconUri":"https://www.bing.com/sa/simg/favicon-2x.ico","alternateText":"bing.com"},"attributionDisplayText":"bing.com"}
ClipboardPayload: N/A
StartTime: 10/21/2021 12:34
EndTime: N/A
Duration: N/A
LastModifiedTime: 10/21/2021 12:34
LastModifiedOnClient: 10/21/2021 12:34
OriginalLastModifiedOnClient: N/A
ExpirationTime: 11/20/2021 12:34
CreatedInCloud: N/A
IsLocalOnly: FALSE – might indicate that activity has been synced
ETag: 2348
PackageIdHash: u/3w0FX2KJ+WP7GPAVoBtwpDkL/07j99Aomf+tLN9wA=
PlatformDeviceId: 8vHQ+SS/rq5UZhpYVOBkGCiZ8zJLOvGrfolxOfJ9+E8=
DevicePlatform: N/A – unfortunately not available: we could find the type of device from which activity came from
TimeZone: N/A
Conclusion
Windows 10 Timeline is an artefact which helps to reveal information about user activity on the system. We can usually find records from last 30 days here. They document operations such as file opening, application execution or web browsing. Thanks to the available tools we can parse and analyze Windows 10 Timeline data efficiently. Despite some aspects of Timeline are not well described, artefact has great potential for forensic investigation. We can link the information about activity to a certain user. Records are preserved in database even after the files and programs related to them had been removed from the system.